Stefaan Verhulst
Article by Virginia Barbour and Martin Borchert: “In the few months since the first case of COVID-19 was identified, the underlying cause has been isolated, its symptoms agreed on, its genome sequenced, diagnostic tests developed, and potential treatments and vaccines are on the horizon. The astonishingly short time frame of these discoveries has only happened through a global open science effort.
The principles and practices underpinning open science are what underpin good research—research that is reliable, reproducible, and has the broadest impact possible. It specifically requires the application of principles and practices that make research FAIR (Findable, Accessible, Interoperable, Reusable); researchers are making their data and preliminary publications openly accessible, and then publishers are making the peer-reviewed research immediately and freely available to all. The rapid dissemination of research—through preprints in particular as well as journal articles—stands in contrast to what happened in the 2003 SARS outbreak when the majority of research on the disease was published well after the outbreak had ended.
Many outside observers might reasonably assume, given the digital world we all now inhabit, that science usually works like this. Yet this is very far from the norm for most research. Science is not something that just happens in response to emergencies or specific events—it is an ongoing, largely publicly funded, national and international enterprise….
Sharing of the underlying data that journal articles are based on is not yet a universal requirement for publication, nor are researchers usually recognised for data sharing.
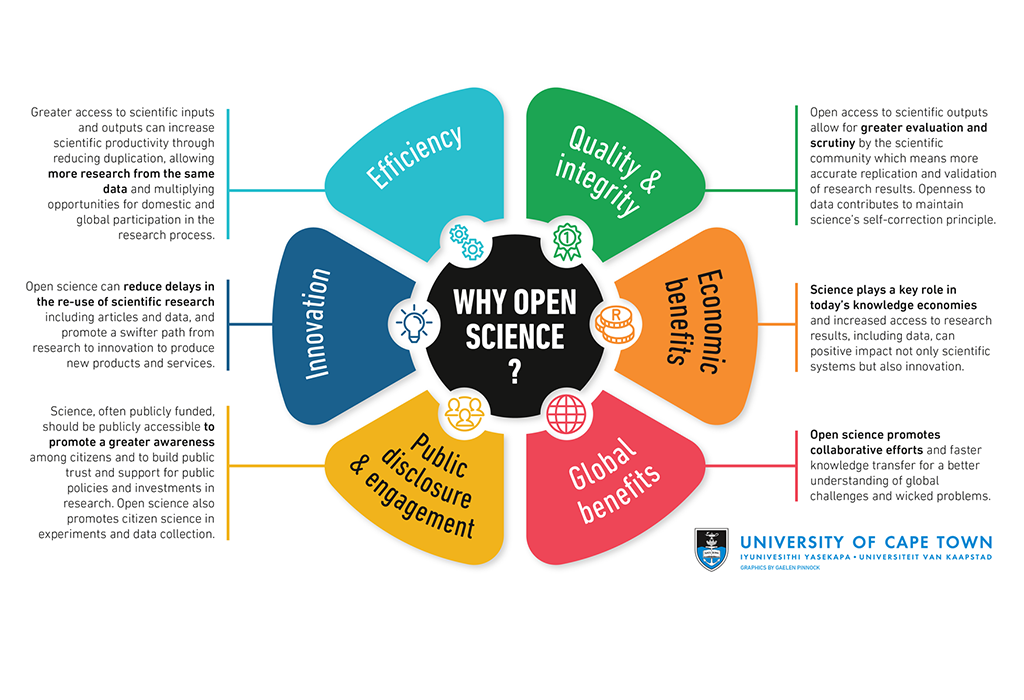
There are many benefits associated with an open science model. Image adapted from: Gaelen Pinnock/UCT; CC-BY-SA 4.0 .
Once published, even access to research is not seamless. The majority of academic journals still require a subscription to access. Subscriptions are expensive; Australian universities alone currently spend more than $300 million per year on subscriptions to academic journals. Access to academic journals also varies between universities with varying library budgets. The main markets for subscriptions to the commercial journal literature are higher education and health, with some access to government and commercial….(More)”.
Article by Peter Baeck and Sophie Reynolds: One of the most prominent examples of how technology and data is being used to empower citizens is happening in Seoul. Here the city has used its ‘citizens as mayors’ philosophy for smart cities; an approach which aims to equip citizens with the same real-time access to information as the mayor. Seoul has gone further than most cities in making information about the COVID-19 outbreak in the city accessible to citizens. Its dashboard is updated multiple times daily and allows citizens to access the latest anonymised information on confirmed patients’ age, gender and dates of where they visited and when, after developing symptoms. Citizens can access even more detailed information; down to visited restaurants and cinema seat numbers.
The goal is to provide citizens with the information needed to take precautionary measures, self-monitor and report if they start showing symptoms after visiting one of the “infection points.” To help allay people’s fears and reduce the stigma associated with businesses that have been identified as “infection points”, the city government also provides citizens with information about the nearest testing clinics and makes “clean zones” (places that have been disinfected after visits by confirmed patients) searchable for users.
In addition to national and institutional responses there are (at least) five ways collective intelligence approaches are helping city governments, companies and urban communities in the fight against COVID-19:
1. Open sharing with citizens about the spread and management of COVID-19:
Based on open data provided by public agencies, private sector companies are using the city as a platform to develop their own real-time dashboards and mobile apps to further increase public awareness and effectively disseminate disease information. This has been the case with Corona NOW, Corona Map, Corona 100m in Seoul, Korea – which allow people to visualise data on confirmed coronavirus patients, along with patients’ nationality, gender, age, which places the patient has visited, and how close citizens are to these coronavirus patients. Developer Lee Jun-young who created the Corona Map app, said he built it because he found that the official government data was too difficult to understand.
Meanwhile in city state Singapore, the dashboard developed by UpCode scrapes data provided by the Singapore Ministry of Health’s own dashboard (which is exceptionally transparent about coronavirus case data) to make it cleaner and easier to navigate, and vastly more insightful. For instance, it allows you to learn about the average recovery time for those infected.
UpCode is making its platform available for others to re-use in other contexts.
2. Mobilising community-led responses to tackle COVID-19
Crowdfunding is being used in a variety of ways to get short-term targeted funding to a range of worthy causes opened up by the COVID-19 crisis. Examples include helping to fundraise for community activities for those directly affected by the crisis, backing tools and products that can address the crisis (such as buying PPE) and pre-purchasing products and services from local shops and artists. A significant proportion of the UK’s 1,000 plus mutual aid initiatives are now turning to crowdfunding as a way to rapidly respond to the new and emerging needs occurring at the city-wide and hyperlocal (i.e. streets and neighbourhood) levels.
Aberdeen City Mutual Aid group set up a crowdfunded community fund to cover the costs of creating a network of volunteers across the city, as well as any expenses incurred at food shops, fuel costs for deliveries and purchasing other necessary supplies. Similarly, the Feed the Heroes campaign was launched with an initial goal of raising €250 to pay for food deliveries for frontline staff who are putting in extra hours at the Mater Hospital, Dublin during the coronavirus outbreak….(More)”.
Bryan Wolff, Yevheniia Berchul, Yu Gong, Andrey Shevlyakov at Strelka Mag: “French philosopher Michel Foucault defined biopower as the power over bodies, or the social and political techniques to control people’s lives. Cameroonian philosopher Achille Mbembe continued this line of thinking to arrive at necropolitics, the politics of death, or as he phrases it: “contemporary forms of subjugation of life, to the power of death.” COVID-19 has put these powers in sharp relief. Most world-changing events of the twenty-first century have been internalized with the question “where were you?” For example, “where were you when the planes hit?” But the pandemic knows no single universal moment to refer to. It’s become as much a question of when, as of where. “When did you take the pandemic seriously?” Most likely, your answer stands in direct relation to your proximity to death. Whether a critical mass or a specific loss, fatality defined COVID-19’s reality.
For many governments, it wasn’t the absolute count of death, but rather its simulations that made them take action. The United States was one of the last countries holding out on a lockdown until the Imperial College report projected the possibility of two million to four million fatalities in the US alone (if no measures were taken). And these weren’t the only simulations being run. A week into the lockdown, it was wondered aloud whether this was all worth the cost. It was a unique public reveal of the deadly economics—or necroeconomics—that we’re usually insulated from, whether through specialist language games or simply because they’re too grim to face. But ignoring the financialization of our demise doesn’t make it go away. If we are to ever reconsider the systems meant to keep us alive, we’d better get familiar. What better place to start than to see the current crisis through the eyes of one of the most widely used models of death: the one that puts a price on life. It’s called the “Value of a Statistical Life” or VSL..(More)”.
Mariana Mazzucato and Giulio Quaggiotto at Project Syndicate: “Decades of privatization, outsourcing, and budget cuts in the name of “efficiency” have significantly hampered many governments’ responses to the COVID-19 crisis. At the same time, successful responses by other governments have shown that investments in core public-sector capabilities make all the difference in times of emergency. The countries that have handled the crisis well are those where the state maintains a productive relationship with value creators in society, by investing in critical capacities and designing private-sector contracts to serve the public interest.
From the United States and the United Kingdom to Europe, Japan, and South Africa, governments are investing billions – and, in some cases, trillions – of dollars to shore up national economies. Yet, if there is one thing we learned from the 2008 financial crisis, it is that quality matters at least as much as quantity. If the money falls on empty, weak, or poorly managed structures, it will have little effect, and may simply be sucked into the financial sector. Too many lives are at stake to repeat past errors.
Unfortunately, for the last half-century, the prevailing political message in many countries has been that governments cannot – and therefore should not – actually govern. Politicians, business leaders, and pundits have long relied on a management creed that focuses obsessively on static measures of efficiency to justify spending cuts, privatization, and outsourcing.
As a result, governments now have fewer options for responding to the crisis, which may be why some are now desperately clinging to the unrealistic hope of technological panaceas such as artificial intelligence or contact-tracing apps. With less investment in public capacity has come a loss of institutional memory (as the UK’s government has discovered) and increased dependence on private consulting firms, which have raked in billions. Not surprisingly, morale among public-sector employees has plunged in recent years.
Consider two core government responsibilities during the COVID-19 crisis: public health and the digital realm. In 2018 alone, the UK government outsourced health contracts worth £9.2 billion ($11.2 billion), putting 84% of beds in care homes in the hands of private-sector operators (including private equity firms). Making matters worse, since 2015, the UK’s National Health Service has endured £1 billion in budget cuts.
Outsourcing by itself is not the problem. But the outsourcing of critical state capacities clearly is, especially when the resulting public-private “partnerships” are not designed to serve the public interest. Ironically, some governments have outsourced so eagerly that they have undermined their own ability to structure outsourcing contracts. After a 12-year effort to spur the private sector to develop low-cost ventilators, the US government is now learning that outsourcing is not a reliable way to ensure emergency access to medical equipment….(More)”.
Seth Reynolds at NPC: “Never has the interdependence of our world been experienced by so many, so directly, so rapidly and so simultaneously. Our response to one threat, Covid-19, has unleashed a deluge of secondary and tertiary consequences that have swept across the globe faster than the virus itself. The butterfly effect has taken on new dimensions, as the reality of system interdependence at multiple levels has been brought directly into our homes and news feeds:
- Individually, an innocuous bus journey sends a stranger to intensive care in a fortnight
- Societally, health charities are warning that actions taken in response to one health crisis – Covid-19 – could lead to up to 11,000 deaths of women in childbirth around the world because of another – namely, 9.5m women not getting access to family planning intervention.
- Governmentally, some systemic consequences of decision-making are there for all to see, while others are less immediately apparent – for example, Trump’s false proclamation of testing availability “for anyone that wants one” ended up actually reducing the availability of tests by immediately increasing demand. It even reduced the already scarce supply of protective masks, which must be disposed of after testing.
Students will be studying coronavirus for years. A systems lens can help us learn essential lessons. Covid-19 has provided many clear examples of effective systemic action, and stark lessons in the consequences of non-systemic thinking. Leaders and decision-makers everywhere are being compelled to think broader and deeper about causation and consequence. Decisions taken, even words spoken, without systemic awareness can have – indeed have had – profoundly damaging effects.
Systemic thinking, planning, action and leadership must now be mainstreamed – individually, organisationally, societally, across public, private and charity sectors. As one American diplomat recently reflected: “from climate change to the coronavirus, complex adaptive systems thinking is key to handling crises”. In fact, some epidemiologists, suddenly the world’s most valuable profession, have been calling for more systemic ways of working for years. However, we currently do not think and act in accordance with how our complex systems function and this has been part of the Covid-19 problem…(More)”.
Congressional Research Service: “In common parlance, the terms propaganda, misinformation, and disinformation are often used interchangeably, often with connotations of deliberate untruths of nefarious origin. In a national security context, however, these terms refer to categories of information that are created and disseminated with different intent and serve different strategic purposes. This primer examines these categories to create a framework for understanding the national security implications of information related to the Coronavirus Disease 2019 (COVID-19) pandemic….(More)”.
Blog by Walter J. Radermacher at Data & Policy: “It is rightly pointed out that in the midst of a crisis of enormous dimensions we needed high quality statistics with utmost urgency, but that instead we are in danger of drowning in an ocean of data and information. The pandemic is accompanied and exacerbated by an infodemic. At this moment, and in this confusion and search for solutions, it seems appropriate to take advice from previous initiatives and draw lessons for the current situation. More than 20 years ago in the United Kingdom, the report “Statistics — A Matter of Trust” laid the foundations for overcoming the previously spreading crisis of confidence through a solidly structured statistical system. This report does not stand alone in international comparison. Rather, it is one of a series of global, European and national measures and agreements which, since the fall of the Berlin Wall in 1989, have strengthened official statistics as the backbone of policy in democratic societies, with the UN Fundamental Statistical Principles and the EU Statistics Code of Practice being prominent representatives. So, if we want to deal with our current difficulties, we should address precisely those points that have emerged as determining factors for the quality of statistics, with the following three questions: What (statistical products, quality profile)? How (methods)? Who (institutions)? The aim must be to ensure that statistical information is suitable for facilitating the resolution of conflicts by eliminating the need to argue about the facts and only about the conclusions to be drawn from them.
In the past, this task would have led relatively quickly to a situation where the need for information would have been directed to official statistics as the preferred provider; this has changed recently for many reasons. On the one hand, there is the danger that the much-cited data revolution and learning algorithms (so-called AI) are presented as an alternative to official statistics (which are perceived as too slow, too inflexible and too expensive), instead of emphasizing possible commonalities and cross-fertilization possibilities. On the other hand, after decades of austerity policies, official statistics are in a similarly defensive situation to that of the public health system in many respects and in many countries: There is a lack of financial reserves, personnel and know-how for the new and innovative work now so urgently needed.
It is therefore required, as in the 1990s, to ask the fundamental question again, namely, do we (still and again) really deserve official statistics as the backbone of democratic decision-making, and if so, what should their tasks be, how should they be financed and anchored in the political system?…(More)”.
Andrej Zwitter & Oskar J. Gstrein at the Journal of International Humanitarian Action: “The use of location data to control the coronavirus pandemic can be fruitful and might improve the ability of governments and research institutions to combat the threat more quickly. It is important to note that location data is not the only useful data that can be used to curb the current crisis. Genetic data can be relevant for AI enhanced searches for vaccines and monitoring online communication on social media might be helpful to keep an eye on peace and security (Taulli n.d.). However, the use of such large amounts of data comes at a price for individual freedom and collective autonomy. The risks of the use of such data should ideally be mitigated through dedicated legal frameworks which describe the purpose and objectives of data use, its collection, analysis, storage and sharing, as well as the erasure of ‘raw’ data once insights have been extracted. In the absence of such clear and democratically legitimized norms, one can only resort to fundamental rights provisions such as Article 8 paragraph 2 of the ECHR that reminds us that any infringement of rights such as privacy need to be in accordance with law, necessary in a democratic society, pursuing a legitimate objective and proportionate in their application.
However as shown above, legal frameworks including human rights standards are currently not capable of effectively ensuring data protection, since they focus too much on the individual as the point of departure. Hence, we submit that currently applicable guidelines and standards for responsible data use in the humanitarian sector should also be fully applicable to corporate, academic and state efforts which are currently enacted to curb the COVID-19 crisis globally. Instead of ‘re-calibrating’ the expectations of individuals on their own privacy and collective autonomy, the requirements for the use of data should be broader and more comprehensive. Applicable principles and standards as developed by OCHA, the 510 project of the Dutch Red Cross, or by academic initiatives such as the Signal Code are valid minimum standards during a humanitarian crisis. Hence, they are also applicable minimum standards during the current pandemic.
Core findings that can be extracted from these guidelines and standards for the practical implementation into data driven responses to COVIC-19 are:
- data sensitivity is highly contextual; one and the same data can be sensitive in different contexts. Location data during the current pandemic might be very useful for epidemiological analysis. However, if (ab-)used to re-calibrate political power relations, data can be open for misuse. Hence, any party supplying data and data analysis needs to check whether data and insights can be misused in the context they are presented.
- privacy and data protection are important values; they do not disappear during a crisis. Nevertheless, they have to be weighed against respective benefits and risks.
- data-breaches are inevitable; with time (t) approaching infinity, the chance of any system being hacked or becoming insecure approaches 100%. Hence, it is not a question of whether, but when. Therefore, organisations have to prepare sound data retention and deletion policies.
- data ethics is an obligation to provide high quality analysis; using machine learning and big data might be appealing for the moment, but the quality of source data might be low, and results might be unreliable, or even harmful. Biases in incomplete datasets, algorithms and human users are abundant and widely discussed. We must not forget that in times of crisis, the risk of bias is more pronounced, and more problematic due to the vulnerability of data subjects and groups. Therefore, working to the highest standards of data processing and analysis is an ethical obligation.
The adherence to these principles is particularly relevant in times of crisis such as now, where they mark the difference between societies that focus on control and repression on the one hand, and those who believe in freedom and autonomy on the other. Eventually, we will need to think of including data policies into legal frameworks for state of emergency regulations, and coordinate with corporate stakeholders as well as private organisations on how to best deal with such crises. Data-driven practices have to be used in a responsible manner. Furthermore, it will be important to observe whether data practices and surveillance assemblages introduced under current circumstances will be rolled back to status quo ante when returning to normalcy. If not, our rights will become hollowed out, just waiting for the next crisis to eventually become irrelevant….(More)”.
Ville Aula at LSE Blogs: “Read the front page of any major newspaper and I guarantee that the latest number of patients who have tested positive for COVID-19 and the number of mortalities will feature heavily. Open your social media accounts and you will quickly encounter graphs that show the mounting numbers of cases in different countries, complemented by modelling projections. These numbers and graphs feed the popular imagination of how well countries are “flattening the curve”, a concept that has brought epidemiological modelling inspired language to everyone’s lips.
Numbers, graphs, and data are thus playing an essential part in how we experience the pandemic. The endless flows of numbers from different countries are meticulously compared with those from others. These comparisons then form the basis to how individual countries are portrayed and ranked in the global pandemic drama.
But, there is also doubt in the air. We distrust the existing numbers and call for ever-more accurate information. For example, there has been a lively debate on how widespread the pandemic has been in China, an issue that connects directly to how tests are administered and cases reported. Equally, numbers from Europe do not provide indisputable or uniform information on the pandemic either, because their collection is subject to vastly different policies, practices, and contexts that make comparisons difficult. We also lack the scientific consensus that would allow us to link the number of mortalities to the prevalence of the virus, yet mortalities are still often taken as the most solid form of information on the pandemic. These doubts have fuelled demands to do systematic population level testing of the virus prevalence, which is just a different way of saying that we need more numbers.
Numbers are thus both the problem and the solution, and we want more of them. However, what makes numbers useful for developing better treatments and policies, does not necessarily lead to the same outcomes when applied to public debate. In the broader sphere of public debate, such tendencies reveal a longing for the veracity of data during times of uncertainty. Even when such calls are founded on demands for transparency in the name of democracy or healthy skepticism of existing data, they are entangled in a faulty logic of data itself eventually providing a solid standing for public debate….(More)”.
Paper by Ugo Pagallo: “The paper examines the legal and political impact of the Covid-19 crisis, drawing the attention to fundamental questions on authority and political legitimacy, coercion and obligation, power and cooperation. National states and sovereign governments have had and still will have a crucial role in re-establishing the public health sector and addressing the colossal challenges of economic re-construction. Scholars have accordingly discussed the set of legal means displayed during this crisis: emergency decrees, lockdowns, travel bans, and generally speaking, powers of the state of exception.
The aim of this paper is to stress the limits of such perspectives on powers of national governments and sovereigns, in order to illustrate what goes beyond such powers. Focus should be on the ontological, epistemic and normative constraints that affect today’s rights and duties of national states. Such constraints correspond to a class of problems that is complex, often transnational, and increasingly data-driven. In addition, we should not overlook the lessons learnt from such fields, as environmental law and internet governance, anti-terrorism and transnational business law, up to the regulation of Artificial Intelligence (AI). Such fields show that legal co-regulation and mechanisms of coordination and cooperation complement the traditional powers of national governments even in the times of the mother of all pandemics. The Covid-19 crisis has been often interpreted as if this were the last chapter of an on-going history about the Leviathan and its bio-powers. It is not. The crisis regards the end of the first chapter on the history of today’s information societies….(More)”.