Blog Post by Ivan Ivanitskiy: “People are resorting to blockchain for all kinds of reasons these days. Ever since I started doing smart contract security audits in mid-2017, I’ve seen it all. A special category of cases is ‘blockchain use’ that seems logical and beneficial, but actually contains a problem that then spreads from one startup to another. I am going to give some examples of such problems and ineffective solutions so that you (developer/customer/investor) know what to do when somebody offers you to use blockchain this way.
1. Supply chain management
Let’s say you ordered some goods, and a carrier guarantees to maintain certain transportation conditions, such as keeping your goods cold. A proposed solution is to install a sensor in a truck that will monitor fridge temperature and regularly transmit the data to the blockchain. This way, you can make sure that the promised conditions are met along the entire route.
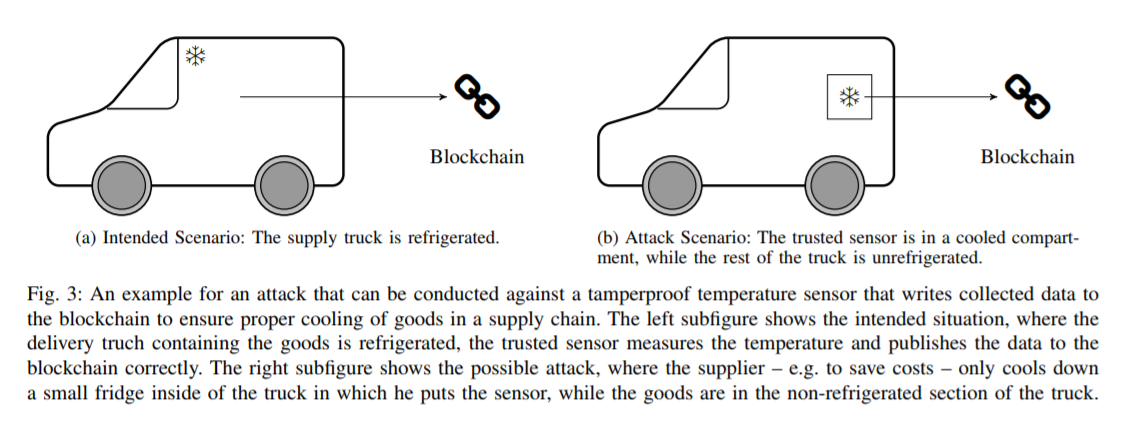
The problem here is not blockchain, but rather sensor, related. Being part of the physical world, the sensor is easy to fool. For example, a malicious carrier might only cool down a small fridge inside the truck in which they put the sensor, while leaving the goods in the non-refrigerated section of the truck to save costs.
I would describe this problem as:
Blockchain is not Internet of Things (IOT).
We will return to this statement a few more times. Even though blockchain does not allow for modification of data, it cannot ensure such data is correct.The only exception is on-chain transactions, when the system does not need the real world, with all necessary information already being within the blockchain, thus allowing the system to verify data (e.g. that an address has enough funds to proceed with a transaction).
Applications that submit information to a blockchain from the outside are called “oracles” (see article ‘Oracles, or Why Smart Contracts Haven’t Changed the World Yet?’ by Alexander Drygin). Until a solution to the problem with oracles is found, any attempt at blockchain-based supply chain management, like the case above, is as pointless as trying to design a plane without first developing a reliable engine.
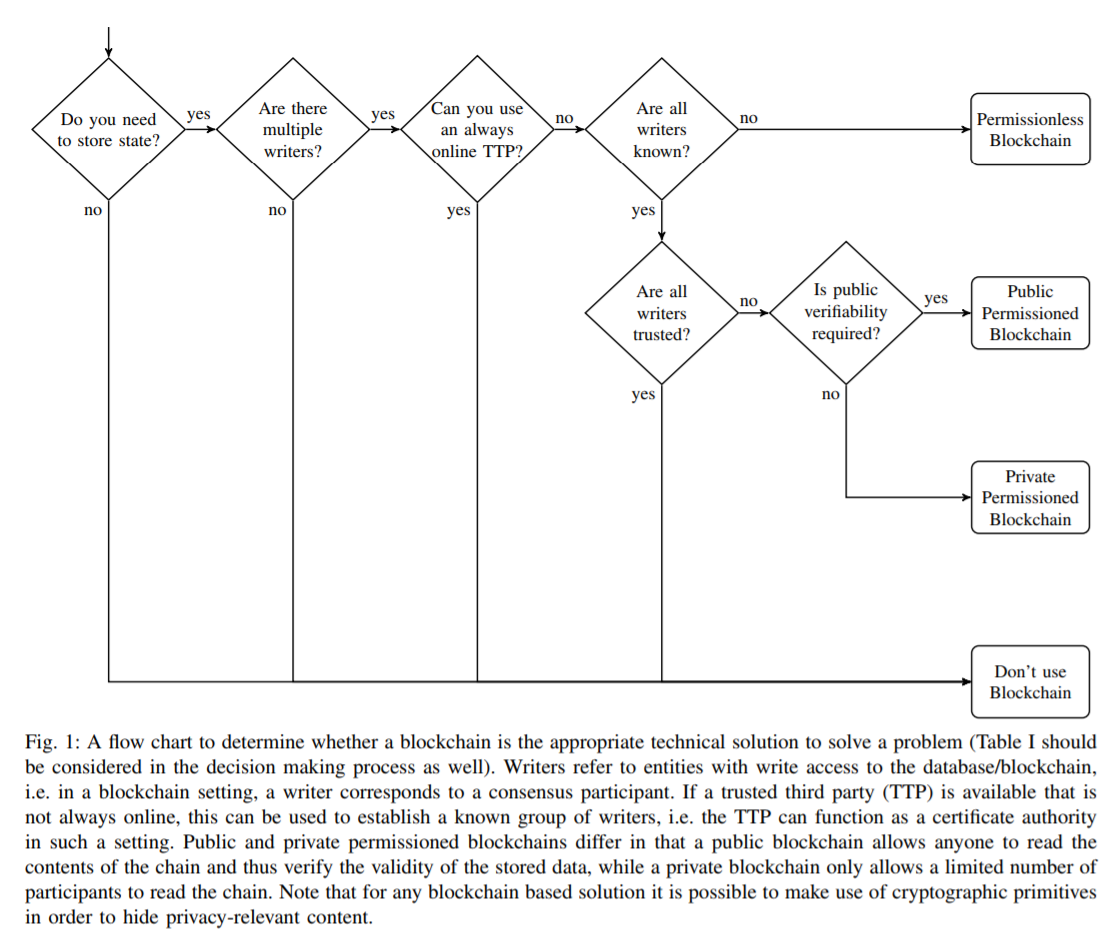
I borrowed the fridge case from the article ‘Do you Need Blockchain’ by Karl Wüst and Arthur Gervais. I highly recommend reading this article and paying particular attention to the following diagram:
2. Object authenticity guarantee
Even though this case is similar to the previous one, I would like to single it out as it is presented in a different wrapper.
Say we make unique and expensive goods, such as watches, wines, or cars. We want our customers to be absolutely sure they are buying something made by us, so we link our wine bottle to a token supported by blockchain and put a QR code on it. Now, every step of the way (from manufacturer, to carrier, to store, to customer) is confirmed by a separate blockchain transaction and the customer can track their bottle online.
However, this system is vulnerable to a very simple threat: a dishonest seller can make a copy of a real bottle with a token, fill it with wine of lower quality, and either steal your expensive wine or sell it to someone who does not care about tokens. Why is it so easy? That’s right! Because…(More)”